AWS Network Firewall
This section has instructions for collecting AWS Network Firewall log messages from AWS S3 and sending them to Sumo Logic to be ingested by CSE.
Step 1: Enable AWS Network Firewall logs
- Follow AWS instructions on firewall log delivery for S3.
- Before configuring collection, you need to grant Sumo Logic permission to access your AWS data. For instructions see Grant Access to an AWS Product.
Step 2: Configure collection
In this step, you configure an HTTP Source to collect AWS Network Firewall messages. You can configure the source on an existing Hosted Collector or create a new collector. If you’re going to use an existing collector, jump to Configure an AWS S3 Source below. Otherwise, create a new collector as described in Configure a hosted collector below, and then create the HTTP Source on the collector.
Configure a Hosted Collector
- In the Sumo Logic platform, select Manage Data > Collection > Collection.
- Click Add Collector.
- Click Hosted Collector.
- The Add Hosted Collector popup appears.
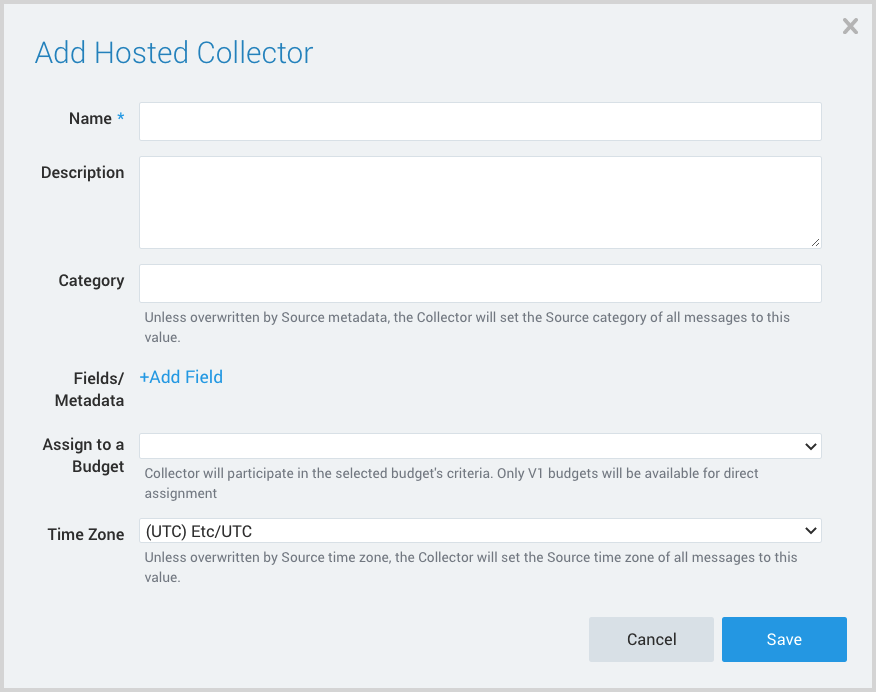
- Name. Provide a Name for the Collector.
- Description. (Optional)
- Category. Enter a string to tag the output collected from the source. The string that you supply will be saved in a metadata field called
_sourceCategory. - Fields.
- If you are planning that all the sources you add to this collector will forward log messages to CSE, click the +Add Field link, and add a field whose name is
_siemForwardand value is true. This will cause the collector to forward all of the logs collected by all of the sources on the collector to CSE. - If all sources in this collector will be AWS Network Firewall sources, add an additional field with key
_parserand value/Parsers/System/AWS/AWS Network Firewall.
- If you are planning that all the sources you add to this collector will forward log messages to CSE, click the +Add Field link, and add a field whose name is
It’s also possible to configure individual sources to forward to CSE, as described in the following section.
Configure an AWS S3 Source
- In Sumo Logic, select Manage Data > Collection > Collection.
- Navigate to the Hosted Collector where you want to create the source.
- On the Collectors page, click Add Source next to a Hosted Collector.
- Select Amazon S3.
- The page refreshes.
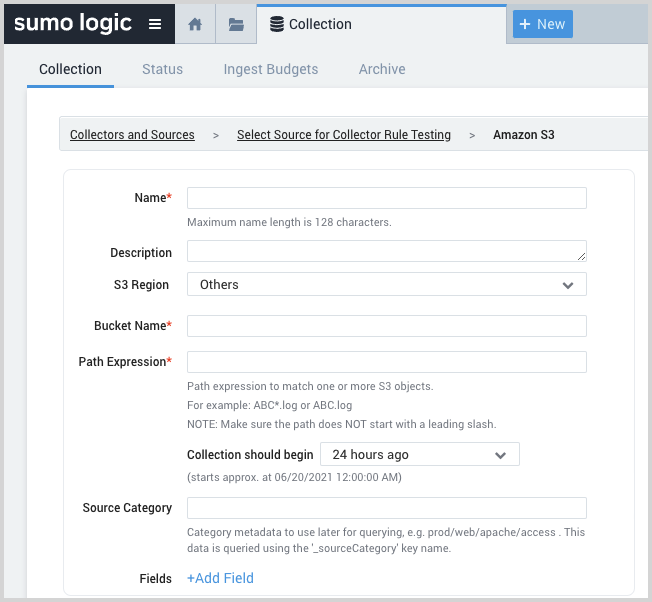
- Name. Enter a name for the source.
- Description. (Optional)
- S3 Region. Choose the AWS Region the S3 bucket resides in.
- Bucket Name. The name of your organizations S3 bucket as it appears in AWS.
- Path Expression. The path expression of the log file(s) in S3, can contain wildcards to include multiple log files.
- Source Category. Enter a string to tag the output collected from the source. The string that you supply will be saved in a metadata field called
_sourceCategory. - Fields.
- If you are not forwarding all sources in the hosted collector to CSE, click the +Add Field link, and add a field whose name is
_siemForwardand value is true. This will ensure all logs for this source are forwarded to CSE. - If you are not parsing all sources in the hosted collector with the same parser, add an additional field named
_parserwith value /Parsers/System/AWS/AWS Network Firewall.
- If you are not forwarding all sources in the hosted collector to CSE, click the +Add Field link, and add a field whose name is
- AWS Access. For AWS Access you have two Access Method options. Select Role-based access or Key access based on the AWS authentication you are providing. Role-based access is preferred. Sumo Logic access to AWS (instructions are provided above in Step 1) is a prerequisite for role-based access.
- Role-based access. Enter the Role ARN that was provided by AWS after creating the role.
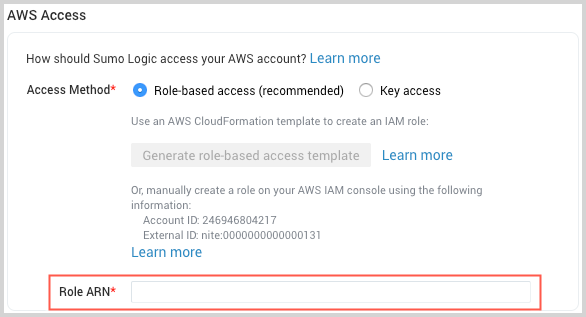
- Key access. Enter the Access Key ID and Secret Access Key. See AWS Access Key ID and AWS Secret Access Key for details.
- Role-based access. Enter the Role ARN that was provided by AWS after creating the role.
- In the Advanced Options for Logs section, uncheck the Detect messages spanning multiple lines option.
- Click Save.
Step 3: Verify ingestion
In this step, you verify that your logs are successfully making it into CSE.
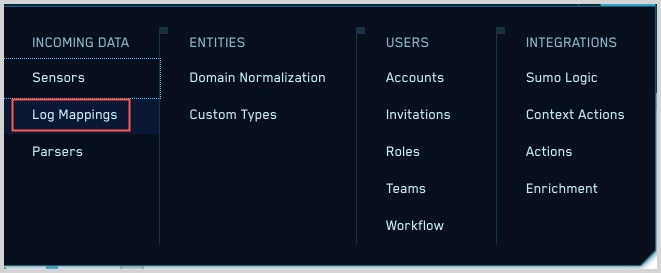
- Click the gear icon, and select Log Mappings under Incoming Data.
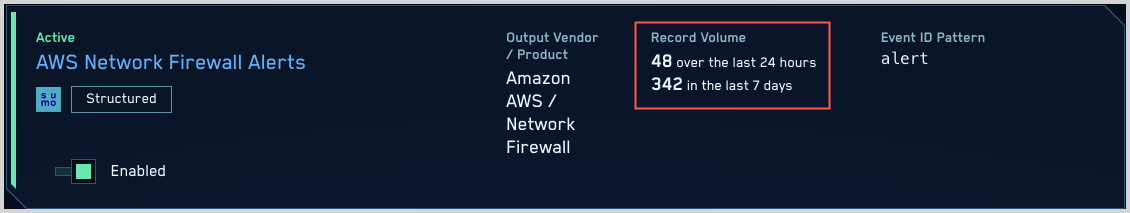
- On the Log Mappings page search for "AWS Network Firewall " and check under Record Volume.
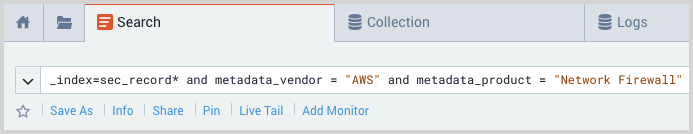
- For a more granular look at the incoming records, you can also search the Sumo Logic platform for AWS Network Firewall security records.