Symantec Endpoint Security

Symantec Endpoint Security safeguards organizations from various network threats and risks. The Sumo Logic app for Symantec Endpoint Security provides visibility into log data by using the Symantec Endpoint Security Service. This service collects and forwards the Symantec Endpoint Security data to Sumo Logic for analysis, offering a comprehensive view of the endpoint security statuses through various widgets. These widgets present essential information, including the number of incidents categorised by type, impacted hosts, malicious files, threat details, and critical or high-severity incidents. The dashboard also highlights potential security vulnerabilities, such as the top 10 affected hosts, IP addresses, and malicious files. This allows administrators to monitor and manage endpoint security in real time, enhancing quick responses to threats. By utilizing the Symantec Endpoint Security Service, organizations can protect their employees' endpoints and enhance their defenses against emerging threats.
This app includes built-in monitors. For details on creating custom monitors, refer to Create monitors for Symantec Endpoint Security app.
Log types
This app uses Symantec Endpoint Security Source to collect the incidents and event logs from the Symantec Endpoint Security platform.
Sample log message
Incident Log
{
"customer_uid": "TEST-JvOsaJktSS-eyL-dXhxOvA",
"incident_uid": "afb07d00-89dd-4813-8e1e-3ed5fa83444d",
"type": "INCIDENT_UPDATE",
"conclusion": "Suspicious Activity",
"remediation": "Change the credentials for accounts which have accessed this endpoint. Employ software whitelisting tools to prevent unauthorized access to the LSASS process and the Windows Registry Security Accounts Manager. Mandate that administrator accounts have unique passwords per system to limit the exposure caused by the theft of credentials. Similarly, avoid the inclusion of user or domain accounts in local administrator groups to limit exposure due to credential theft associated with such accounts.",
"priority_id": 4,
"category_id": 1,
"modified": "2023-04-26T23:38:48.634+00:00",
"state_id": 1,
"id": 4,
"product_uid": "31B0C880-0229-49E8-94C5-48D56B1BD7B9",
"device_time": 1682552328634,
"ref_incident_uid": 102106,
"rule_name": "Advanced Attack Technique",
"created": "2023-04-26T15:44:19.345+00:00",
"type_id": 8076,
"incident_url": "https://sep.securitycloud.symantec.com/v2/incidents/incidentListing/afb07d00-89dd-4813-8e1e-3ed5fa83444d/details",
"message": "OS Credential Dumping",
"version": "1.0",
"product_name": "Symantec Integrated Cyber Defense Manager",
"event_id": 80760004,
"domain_uid": "TEST-ZBg_IqnyTAijNjP2BOOcuw",
"detection_type": "Advanced Analytics",
"severity_id": 4,
"time": 1682552328634,
"suspected_breach": "Yes"
}
Event Log
{
"customer_uid": "TEST-JvOsaJktSS-eyL-dXhxOvA",
"incident_uid": "6af35ed1-ee4a-463a-a40d-dde000dead84",
"type": "INCIDENT_CREATION",
"conclusion": "Malicious File",
"remediation": "You can isolate the endpoint(s), remove the file(s) and/or clean the system(s).",
"priority_id": 4,
"category_id": 1,
"modified": "2023-04-26T21:01:13.426+00:00",
"state_id": 1,
"id": 4,
"product_uid": "31B0C880-0229-49E8-94C5-48D56B1BD7B9",
"events": [
{
"type_id": 8031,
"type": "sandbox_file_detection",
"id": 14,
"message": "Sandbox result for the 'Chrome.exe' file is malicious.",
"user_name": "SYSTEM",
"device_uid": "KLXOjk4ET-CeJZBA3iipkw",
"device_name": "Victim-1",
"device_time": "2023-04-26T21:01:09.003Z",
"severity_id": 5,
"category_id": 1,
"feature_uid": "3F3DC574-02A7-11E9-8EB2-F2801F1B9FD1",
"product_uid": "E3A8F790-52A2-4BE3-87D7-93698CDDD021",
"status_detail": "File is malicious",
"command_uid": "365f1e54-8cb6-4d6c-9478-078e456709e3",
"status_id": 1,
"device_ip": "172.28.53.29",
"device_os_name": "Windows 10 Professional Edition",
"device_domain": "evilcorp.com",
"product_ver": "14.3.9513.7000",
"customer_uid": "TEST-JvOsaJktSS-eyL-dXhxOvA",
"domain_uid": "TEST-ZBg_IqnyTAijNjP2BOOcuw",
"ref_uid": "2e080e9a-791f-33fd-90b7-de575f267025",
"threat": {
"provider": "Cynic",
"type_id": 5,
"name": "Threat Detected By Cynic",
"risk_id": 100,
"id": 0
},
"file": {
"path": "C:\\Users\\edradmin\\Desktop\\Chrome.exe",
"name": "Chrome.exe",
"sha2": "39fff7c11c59ce946cfec471d99baaa832266a07ab6f30cd123e385ca9436efa"
},
"version": "1.0",
"product_name": "Symantec Endpoint Detection and Response",
"feature_name": "Endpoint Detection and Response",
"feature_ver": "1.0",
"edr_event_data_type": "malicious",
"event_data_type": "sep",
"user": {
"name": "SYSTEM"
},
"time": "2023-04-26T21:01:09.003Z",
"timezone": 0,
"log_time": "2023-04-26T21:01:11.285Z",
"uuid": "8031:77c48db0-e475-11ed-d50e-0000633d5a56",
"log_name": "event_service_6_t2_2023-04-26"
}
],
"device_time": 1682542873426,
"ref_incident_uid": 102108,
"rule_name": "Critical Cynic Detections",
"created": "2023-04-26T21:01:13.426+00:00",
"type_id": 8075,
"incident_url": "https://sep.securitycloud.symantec.com/v2/incidents/incidentListing/6af35ed1-ee4a-463a-a40d-dde000dead84/details",
"message": "Sandbox detection: Chrome.exe",
"version": "1.0",
"product_name": "Symantec Integrated Cyber Defense Manager",
"event_id": 80750004,
"domain_uid": "TEST-ZBg_IqnyTAijNjP2BOOcuw",
"detection_type": "Sandbox",
"severity_id": 5,
"time": 1682542873426,
"suspected_breach": "No"
}
Sample queries
_sourceCategory="Labs/SES" !device_uid
| json "incident_uid", "type", "severity_id", "priority_id", "category_id", "conclusion", "detection_type", "state_id", "suspected_breach", "created", "modified", "message", "incident_url", "rule_name", "product_name", "remediation" as incident_uid, type, severity, priority, category, conclusion, detection_type, state, suspected_breach, created_timestamp, modified_timestamp, message, incident_url, rule_name, product_name, remediation nodrop
| if (severity in ("1", "2", "6") , "Reserved", if (severity matches "3", "Minor", if (severity matches "4", "Major", if (severity matches "5", "Critical", "Other")))) as severity
| if (category matches "1", "Security", "Other") as category
| if (state matches "0" , "Unknown", if (state matches "1", "New", if (state matches "2", "In Progress", if (state matches "3", "On Hold", if (state matches "4", "Resolved", if (state matches "5", "Closed", "Other")))))) as state
// global filters
| where severity matches "{{severity}}"
| where category matches "{{category}}"
| where type matches "{{type}}"
| where state matches "{{state}}"
| where conclusion matches "{{conclusion}}"
| count by incident_uid, severity
| count by severity
| sort by _count, severity
_sourceCategory="Labs/SES" !device_uid
| json "incident_uid", "type", "severity_id", "priority_id", "category_id", "conclusion", "detection_type", "state_id", "suspected_breach", "created", "modified", "message", "incident_url", "rule_name", "product_name", "remediation" as incident_uid, type, severity, priority, category, conclusion, detection_type, state, suspected_breach, created_timestamp, modified_timestamp, message, incident_url, rule_name, product_name, remediation nodrop
| if (severity in ("1", "2", "6") , "Reserved", if (severity matches "3", "Minor", if (severity matches "4", "Major", if (severity matches "5", "Critical", "Other")))) as severity
| if (category matches "1", "Security", "Other") as category
| if (state matches "0" , "Unknown", if (state matches "1", "New", if (state matches "2", "In Progress", if (state matches "3", "On Hold", if (state matches "4", "Resolved", if (state matches "5", "Closed", "Other")))))) as state
// global filters
| where severity matches "{{severity}}"
| where category matches "{{category}}"
| where type matches "{{type}}"
| where state matches "{{state}}"
| where conclusion matches "{{conclusion}}"
| timeslice 1d
| count by incident_uid, state, _timeslice
| count as frequency by _timeslice, state
| fillmissing timeslice, values all in state
| transpose row _timeslice column state
_sourceCategory="Labs/SES" device_uid
| json "events", "incident_uid", "type", "conclusion", "rule_name", "message", "suspected_breach", "detection_type", "product_name", "incident_url" as events, incident_uid, incident_type, incident_conclusion, incident_rule_name, incident_message, suspected_breach, detection_type, incident_product_name, incident_url
| parse regex field=events "(?<event>\{(?:[^\{\}]|\{[^\{\}]*\})*\})" multi
| json field=event "uuid", "severity_id", "category_id", "type", "edr_event_data_type", "device_name", "user_name", "file.name", "file.path", "file.sha2", "device_uid", "device_ip", "device_os_name", "device_domain", "threat.id", "threat.type_id", "threat.name", "threat.risk_id", "threat.provider", "message", "type_id", "status_detail", "product_name", "feature_name" as uuid, severity, category, type, edr_event_type, device_name, user_name, file_name, file_path, file_sha2, device_uid, device_ip, device_os_name, device_domain, threat_id, threat_type_id, threat_name, threat_risk_id, threat_provider, message, type_id, status_detail, product_name, feature_name nodrop
| if (severity in ("1", "2", "6") , "Reserved", if (severity matches "3", "Minor", if (severity matches "4", "Major", if (severity matches "5", "Critical", "Other")))) as severity
| if (category matches "1", "Security", "Other") as category
// global filters
| where severity matches "{{severity}}"
| where category matches "{{category}}"
| where type matches "{{type}}"
| where user_name matches "{{user_name}}"
| where device_name matches "{{device_name}}"
| where !isBlank(device_name)
| count by device_name, uuid
| count as frequency by device_name
| sort by frequency, device_name
| limit 10
Collection configuration and app installation
Depending on the set up collection method, you can configure and install the app in three ways:
- Create a new collector and install the app. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app, or
- Use an existing collector and install the app. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app, or
- Use existing source and install the app. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
Use the Cloud-to-Cloud Integration for Symantec Endpoint Security Source to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Symantec Endpoint Security app is properly integrated and configured to collect and analyze your Symantec Endpoint Security data.
Create a new collector and install the app
To set up collection and install the app, do the following:
Next-Gen App: To install or update the app, you must be an account administrator or a user with Manage Apps, Manage Monitors, Manage Fields, Manage Metric Rules, and Manage Collectors capabilities depending upon the different content types part of the app.
- Select App Catalog.
- In the 🔎 Search Apps field, run a search for your desired app, then select it.
- Click Install App.
note
Sometimes this button says Add Integration.
- In the Set Up Collection section of your respective app, select Create a new Collector.
- Collector Name. Enter a Name to display the Source in the Sumo Logic web application. The description is optional.
- Timezone. Set the default time zone when it is not extracted from the log timestamp. Time zone settings on Sources override a Collector time zone setting.
- (Optional) Metadata. Click the +Add Metadata link to add a custom log Metadata Fields. Define the fields you want to associate, each metadata field needs a name (key) and value.
 A green circle with a checkmark is shown when the field exists and is enabled in the Fields table schema.
A green circle with a checkmark is shown when the field exists and is enabled in the Fields table schema. An orange triangle with an exclamation point is shown when the field doesn't exist, or is disabled in the Fields table schema. In this case, you'll see an option to automatically add or enable the nonexistent fields to the Fields table schema. If a field is sent to Sumo Logic but isn’t present or enabled in the schema, it’s ignored and marked as Dropped.
An orange triangle with an exclamation point is shown when the field doesn't exist, or is disabled in the Fields table schema. In this case, you'll see an option to automatically add or enable the nonexistent fields to the Fields table schema. If a field is sent to Sumo Logic but isn’t present or enabled in the schema, it’s ignored and marked as Dropped.
- Click Next.
- Configure the source as specified in the
Infobox above, ensuring all required fields are included. - In the Configure section of your respective app, complete the following fields.
- Field Name. If you already have collectors and sources set up, select the configured metadata field name (eg _sourcecategory) or specify other custom metadata (eg: _collector) along with its metadata Field Value.
- Click Next. You will be redirected to the Preview & Done section.
Post-installation
Once your app is installed, it will appear in your Installed Apps folder, and dashboard panels will start to fill automatically.
Each panel slowly fills with data matching the time range query received since the panel was created. Results will not immediately be available but will be updated with full graphs and charts over time.
Use an existing collector and install the app
To set up the source in the existing collector and install the app, do the following:
Next-Gen App: To install or update the app, you must be an account administrator or a user with Manage Apps, Manage Monitors, Manage Fields, Manage Metric Rules, and Manage Collectors capabilities depending upon the different content types part of the app.
- Select App Catalog.
- In the 🔎 Search Apps field, run a search for your desired app, then select it.
- Click Install App.
note
Sometimes this button says Add Integration.
- In the Set Up Collection section of your respective app, select Use an existing Collector.
- From the Select Collector dropdown, select the collector that you want to set up your source with and click Next.
- Configure the source as specified in the
Infobox above, ensuring all required fields are included. - In the Configure section of your respective app, complete the following fields.
- Field Name. If you already have collectors and sources set up, select the configured metadata field name (eg _sourcecategory) or specify other custom metadata (eg: _collector) along with its metadata Field Value.
- Click Next. You will be redirected to the Preview & Done section.
Post-installation
Once your app is installed, it will appear in your Installed Apps folder, and dashboard panels will start to fill automatically.
Each panel slowly fills with data matching the time range query received since the panel was created. Results will not immediately be available but will be updated with full graphs and charts over time.
Use an existing source and install the app
To skip collection and only install the app, do the following:
Next-Gen App: To install or update the app, you must be an account administrator or a user with Manage Apps, Manage Monitors, Manage Fields, Manage Metric Rules, and Manage Collectors capabilities depending upon the different content types part of the app.
- Select App Catalog.
- In the 🔎 Search Apps field, run a search for your desired app, then select it.
- Click Install App.
note
Sometimes this button says Add Integration.
- In the Set Up Collection section of your respective app, select Skip this step and use existing source and click Next.
- In the Configure section of your respective app, complete the following fields.
- Field Name. If you already have collectors and sources set up, select the configured metadata field name (eg _sourcecategory) or specify other custom metadata (eg: _collector) along with its metadata Field Value.
- Click Next. You will be redirected to the Preview & Done section.
Post-installation
Once your app is installed, it will appear in your Installed Apps folder, and dashboard panels will start to fill automatically.
Each panel slowly fills with data matching the time range query received since the panel was created. Results will not immediately be available but will be updated with full graphs and charts over time.
Viewing the Symantec Endpoint Security dashboards
All dashboards have a set of filters that you can apply to the entire dashboard. Use these filters to drill down and examine the data to a granular level.
- You can change the time range for a dashboard or panel by selecting a predefined interval from a drop-down list, choosing a recently used time range, or specifying custom dates and times. Learn more.
- You can use template variables to drill down and examine the data on a granular level. For more information, see Filtering Dashboards with Template Variables.
- Most Next-Gen apps allow you to provide the scope at the installation time and are comprised of a key (
_sourceCategoryby default) and a default value for this key. Based on your input, the app dashboards will be parameterized with a dashboard variable, allowing you to change the dataset queried by all panels. This eliminates the need to create multiple copies of the same dashboard with different queries.
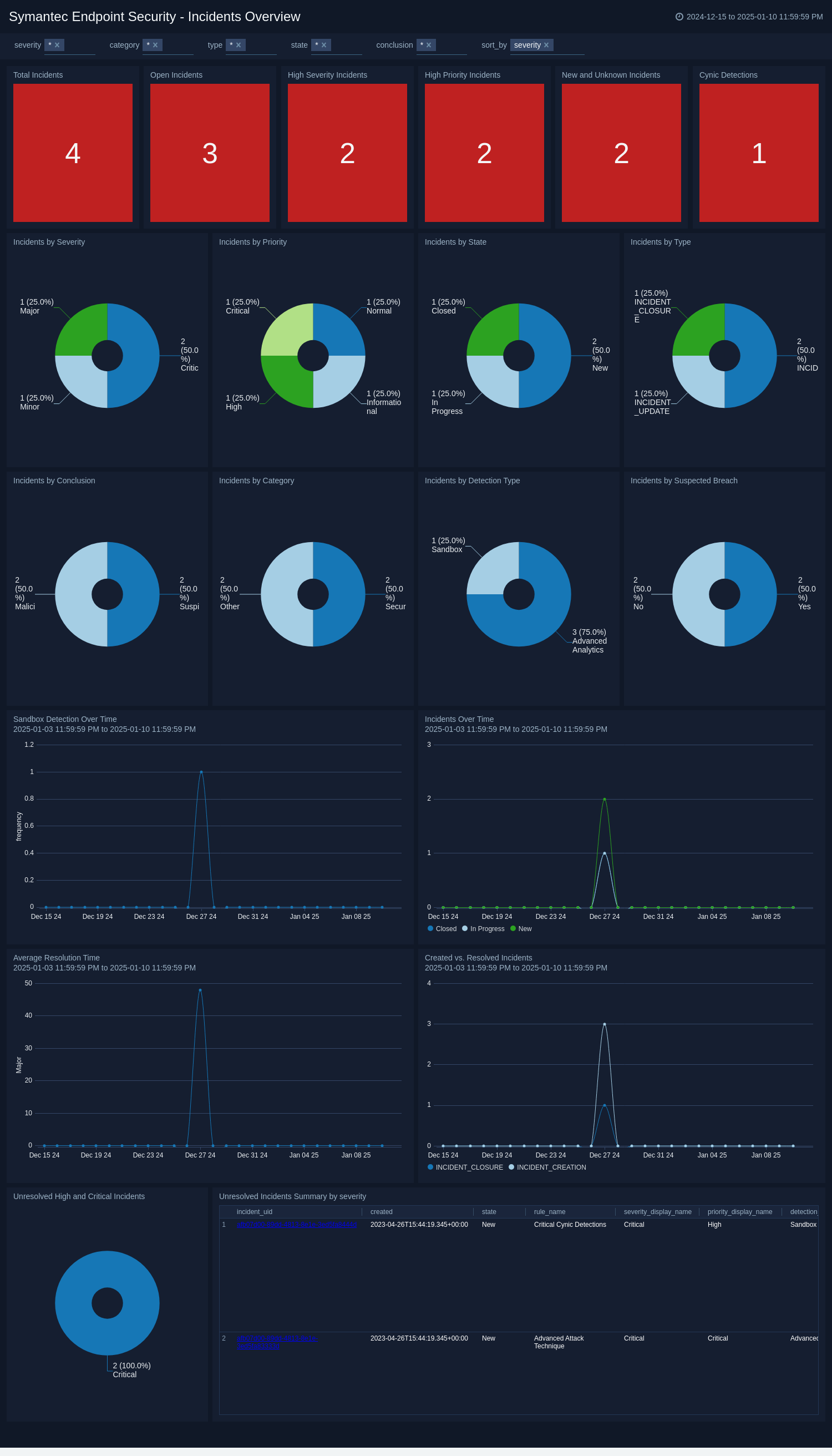
Incidents Overview
The Symantec Endpoint Security - Incidents Overview dashboard provides details on security incidents, their severity, priority, and current status across your endpoint environment.
Use this dashboard to:
- Quickly assess the overall security posture by viewing the number of total, open, high severity, and high priority incidents.
- Identify trends in incident types and categories to focus on areas requiring immediate attention or process improvements.
- Monitor incident resolution times and track the progress of open incidents to ensure timely response and remediation.
- Prioritize incidents by severity and priority to allocate resources effectively and address the most critical threats first.
- Analyze the distribution of incidents across different states and detection types to understand the lifecycle of security events in your environment.
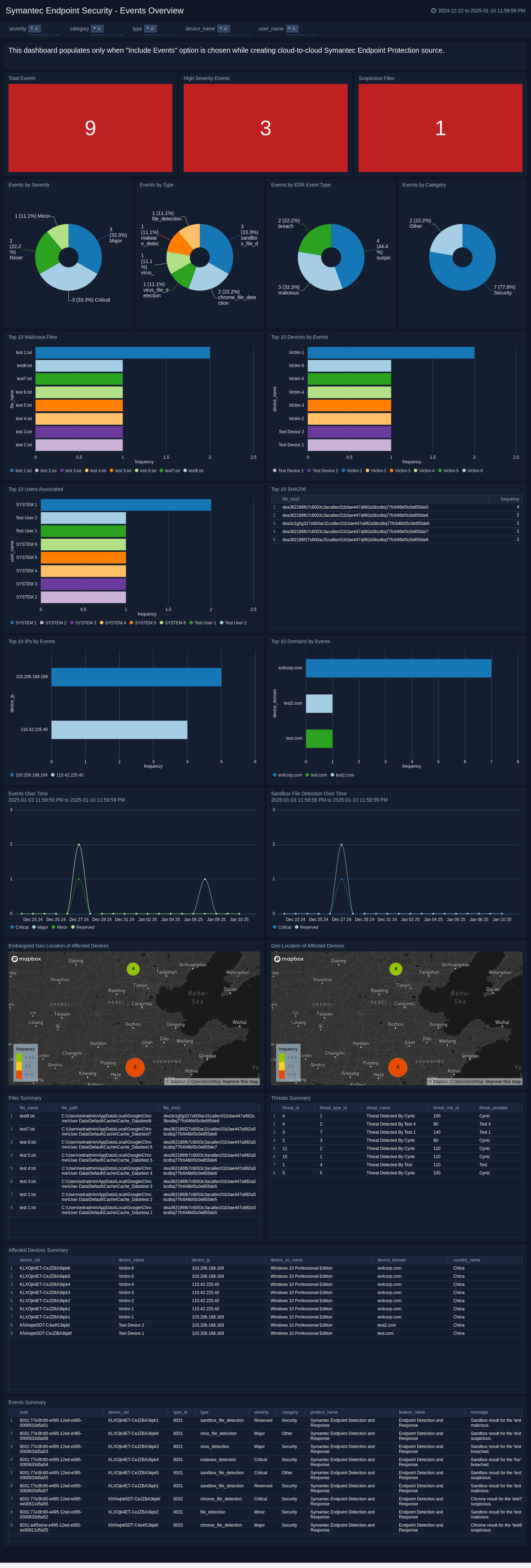
Events Overview
The Symantec Endpoint Security - Events Overview dashboard provides details on security events, their severity, types, and geographical distribution across the protected endpoints.
Use this dashboard to:
- Quickly assess the overall security posture by viewing the total events, high severity events, and suspicious files counts at the top of the dashboard.
- Analyze event trends over time and identify peak periods of security incidents using the Events Over Time graph.
- Identify the most affected devices, allowing for targeted investigation and remediation of compromised assets.
- Visualize the geographical distribution of affected devices and event locations to detect potential regional attack patterns or vulnerabilities.
Create monitors for Symantec Endpoint Security app
From your App Catalog:
- From the Sumo Logic navigation, select App Catalog.
- In the Search Apps field, search for and then select your app.
- Make sure the app is installed.
- Navigate to What's Included tab and scroll down to the Monitors section.
- Click Create next to the pre-configured monitors. In the create monitors window, adjust the trigger conditions and notifications settings based on your requirements.
- Scroll down to Monitor Details.
- Under Location click on New Folder.
note
By default, monitor will be saved in the root folder. So to make the maintenance easier, create a new folder in the location of your choice.
- Enter Folder Name. Folder Description is optional.
tip
Using app version in the folder name will be helpful to determine the versioning for future updates.
- Click Create. Once the folder is created, click on Save.
Symantec Endpoint Security monitors
| Name | Description | Trigger Type (Critical / Warning / MissingData) | Alert Condition |
|---|---|---|---|
Devices With Multiple Incidents | This alert is triggered when a device is associated with multiple incidents. It helps you to monitor and stop potentially harmful devices, enhancing your ability to identify suspicious activity. | Critical | Count > 0 |
File Execution in Suspicious Path | This alert is triggered when some file activity happens from the suspicious file path. It helps you to monitor activity from unusual or suspicious file paths, enhancing your ability to identify suspicious activity. | Critical | Count > 0 |
High Priority or Severity Incidents Detected | This alert is triggered when an incident is created with high priority or severity. It helps you to monitor and stop potentially harmful events that could compromise endpoint security. | Critical | Count > 0 |
High-Risk Threat Detected by Cynic | This alert is triggered when a high-risk threat is detected by the cynic. It allows you to quickly identify endpoints with a high concentration of threat activity, enabling swift action to contain and remediate potential infections. | Critical | Count > 0 |
Hight-Severity Malicious File Detected | This alert is triggered when a known malicious file with high severity is detected running on a device. It helps you to monitor and stop potentially harmful files that could compromise device security and network integrity. | Critical | Count > 0 |
Incidents Detected from Embargoed Locations | This alert is triggered when an incident is detected from a location identified as high-risk. This helps you to monitor incidents from unusual or restricted geographic locations, enhancing your ability to identify suspicious activity. | Critical | Count > 0 |
Sandbox Malicious File Detected | This alert is triggered when a known malicious file is detected by the sandbox. It helps you to monitor and stop potentially harmful files that could compromise device security and network integrity. | Critical | Count > 0 |
Spike in Impacted Devices Count | This alert is triggered when a spike is detected in the number of impacted devices. It helps you to monitor and stop potentially harmful devices, enhancing your ability to identify suspicious activity. | Critical | Count > 0 |
Unresolved Incident Aging Beyond 7 days | This alert is triggered when an incident is created and remains unresolved for 7 days. It helps you to monitor pending incidents for an extended period, enhancing your ability to identify suspicious activity. | Critical | Count > 0 |
Upgrade/Downgrade the Symantec Endpoint Security app (Optional)
To update the app, do the following:
Next-Gen App: To install or update the app, you must be an account administrator or a user with Manage Apps, Manage Monitors, Manage Fields, Manage Metric Rules, and Manage Collectors capabilities depending upon the different content types part of the app.
- Select App Catalog.
- In the Search Apps field, search for and then select your app.
Optionally, you can identify apps that can be upgraded in the Upgrade available section. - To upgrade the app, select Upgrade from the Manage dropdown.
- If the upgrade does not have any configuration or property changes, you will be redirected to the Preview & Done section.
- If the upgrade has any configuration or property changes, you will be redirected to the Setup Data page.
- In the Configure section of your respective app, complete the following fields.
- Field Name. If you already have collectors and sources set up, select the configured metadata field name (eg _sourcecategory) or specify other custom metadata (eg: _collector) along with its metadata Field Value.
- Click Next. You will be redirected to the Preview & Done section.
Post-update
Your upgraded app will be installed in the Installed Apps folder and dashboard panels will start to fill automatically.
See our Release Notes changelog for new updates in the app.
To revert the app to a previous version, do the following:
- Select App Catalog.
- In the Search Apps field, search for and then select your app.
- To version down the app, select Revert to < previous version of your app > from the Manage dropdown.
Uninstalling the Symantec Endpoint Security app (Optional)
To uninstall the app, do the following:
- Select App Catalog.
- In the 🔎 Search Apps field, run a search for your desired app, then select it.
- Click Uninstall.